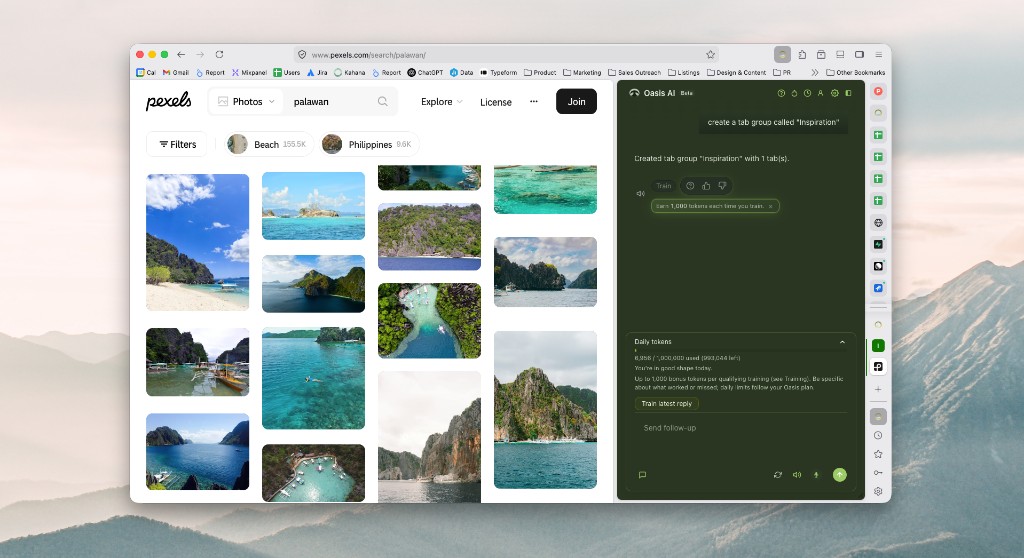
Tabs and windows
Tab and window management
List, open, close, move, and organize tabs and windows without digging through menus.
Example prompts
- What tabs do I have open?
- Close the tab about…
- Open this URL in a new tab
Managed SaaS access, governance in the session, and how to evaluate Oasis next to your IdP and DLP programs
Most enterprise work now runs in the browser: SaaS, internal web apps, and increasingly AI-assisted workflows. Yet many security models still assume corporate laptops, VPNs, and network perimeters as the primary control points. When contractors and partners work from devices you do not own, that mismatch shows up as slow onboarding, policy gaps, or an expensive default to shipping hardware and standing up hosted desktops for roles that mostly live in a handful of web apps.
A managed enterprise browser is one answer to the gap: place governance where work actually happens, inside the browser session, and connect it to the identity and data-protection investments you already have. Oasis is built for that pattern: unified browser policy, IdP-backed sessions, and enterprise DLP alignment where your stack supports browser-level enforcement.
Below you will see the same session-governance visuals and capability blocks we use on the Oasis Enterprise Browser product page, plus evaluation topics for your team: benefits, deployment, UX, and FAQs framed with honest limits (what belongs in a browser vs what still needs other delivery models). For the personal AI browser experience, see Oasis Browser.
Illustrative controls and capability layouts match the live product story: session-level visibility, device vs browser tradeoffs, and four enterprise outcomes with links to deeper feature pages.
| Severity | Title | User | App | Status |
|---|---|---|---|---|
| Critical | Internal roadmap pasted into AI | Jordan Lee | Grok | New |
| Critical | Source code shared to ChatGPT | Alex Chen | ChatGPT | New |
| High | Customer PII pasted into Claude | Morgan Taylor | Claude | In progress |
| High | Unknown AI tool detected | Sam Rivera | Unknown AI | New |
| Medium | Financial data shared to assistant | Jordan Kim | Gemini | Resolved |
Go deeper on Oasis Enterprise
Prefer the full story? Oasis Enterprise Browser overview
SaaS, internal web apps, and AI tools run in sessions that sit beyond classic device-only assumptions. Oasis treats that session as a first-class place for policy.
Four capabilities map to how security and IT teams describe the job: external access, consistent governance, stack integration, and operational speed for web-first work.
Partner and contractor work keeps landing in the browser, often on third-party devices you never issued. Oasis is a managed enterprise browser so unified browser policies and SaaS access expectations can meet people where sessions actually run—without treating hardware logistics as the only answer for every web-first role.
Governance in the browser matters because if policy only follows a managed endpoint image, SaaS on unmanaged or partner-owned devices quietly drifts outside the same enforcement plane. Oasis applies unified browser governance so policies follow the session—what “good” means for extensions, data handling, and app access travels with it.
Identity and DLP together answer who is in the session and what sensitive information is allowed to do. Oasis is designed so those investments extend into SaaS and web workflows instead of stopping where classic network boundaries used to.
When every new contractor waits on imaging or a fresh hosted desktop seat, calendar time stacks up, especially for roles that mostly live in a handful of SaaS apps. A managed enterprise browser with governed sessions can shorten time-to-productivity when your program allows identity-driven SaaS access instead of linear device logistics alone.
Buying-committee lenses for managed browser programs
This page is written for teams evaluating secure SaaS access on corporate and third-party devices. End-user productivity features for the personal browser live on Oasis Browser; the sections below map common questions by stakeholder.
Session governance, data handling, and AI usage in the browser; how policies follow external and contractor sessions; how Oasis complements IdP and DLP rather than replacing your stack.
Delivery models, identity integration, logging, and where a managed browser reduces reliance on hardware logistics or hosted desktops for web-first roles (without promising every workload moves to a tab).
Contractor onboarding speed, project kickoff friction, and operational cost of default laptop or VDI patterns when the real work is SaaS in the browser.
Themes that show up in security, IT, and program reviews
Give external collaborators a path to sanctioned apps with identity, session, and data expectations that match corporate-grade posture.
Apply browser-level policy from a single place for corporate and third-party contexts instead of hoping consumer defaults behave the same everywhere.
Reduce trade-offs between speed, cost, and control by meeting people where they work: the browser.
Key advantages of choosing Oasis for your organization
A managed enterprise browser is one layer in a modern program: it can unify browser expectations for SaaS and web work, extend identity and DLP into sessions on third-party devices, and reduce how often hardware logistics or hosted desktops are the default answer for roles that are already web-first. It does not replace every legacy app or air-gapped workflow.
Enhanced data protection and DLP (controls on copy/paste, download, printing, screenshots, watermarking).
Built‑in threat detection and prevention for phishing, malware, risky sites, and malicious downloads.
Identity-aware access to SaaS and internal web apps from the browser, which can reduce reliance on VPN and VDI for browser-centric roles when your architecture supports it.
New elegant workflows that adapt to how you work, with spatial organization and intuitive controls that reduce cognitive load and improve focus.
Simplified IT operations by consolidating multiple security agents and web security products into the browser layer.
Potential to lower infrastructure and licensing pressure where browser-governed access replaces some VPN, VDI, or parallel web-gateway patterns. Scope depends on workloads and procurement.
Third-party reporting continues to tie incidents to browser factors, phishing, and supply-chain paths. Use these as directional context in your own risk reviews, not as vendor-specific promises.
Share of incidents where browser-related factors appear in industry incident research.
Source: Palo Alto Networks, 2024Year-over-year increase in zero-hour phishing called out in browser security reporting.
Source: Menlo Security, 2025Of breaches involved a third party, including data custodians, third-party software issues, or other supply chain paths, in DBIR analysis.
Source: Verizon, 2024Seamless authentication with your existing identity providers
What to expect when deploying Oasis in your organization
Most teams pilot with a bounded user group, align IdP and DLP assumptions early, and expand policy coverage as confidence grows. Timelines depend on change management, app inventory, and regulatory context; plan proof points with your program office rather than assuming a fixed go-live window.
Oasis seamlessly connects with your current identity provider using industry-standard protocols including SAML, OAuth, and SCIM for user provisioning and authentication.
Deploy through your existing device management platform (VMware Workspace ONE, Citrix Endpoint Management, etc.) or provide a secure download link for self-service installation. The process is straightforward: download, install, and start using.
Team members authenticate through your existing identity system and can instantly import their bookmarks, saved passwords, and browser preferences for a familiar experience.
Begin with a pilot group and specific applications to develop policies that match your workflows. As you gain experience, expand to additional teams and use cases to build comprehensive security coverage.
AI, voice, and calm UX
The same client experience as Oasis Browser, including voice, assistant, confirmations, onboarding, import, and planned Amplifier feedback, ships in Oasis Enterprise Browser. What follows are the live product mocks from the consumer page; enterprise wraps them with policy, identity, and data controls.
Voice
Tap the microphone in the composer to open a focused voice session: a cinematic overlay with an aura visualization, capture modes (Continuous vs Precise), and whether replies are spoken or streamed into chat. Voice and typing share the same assistant thread.
Voice is available in supported builds and may require device permissions. Unavailable builds show a clear in-product message.
Status hints like "Listening" and "Pause briefly after you speak" mirror what you see in the product during capture.
Voice session
Listening
Pause briefly after you speak, or tap the orb to send now.
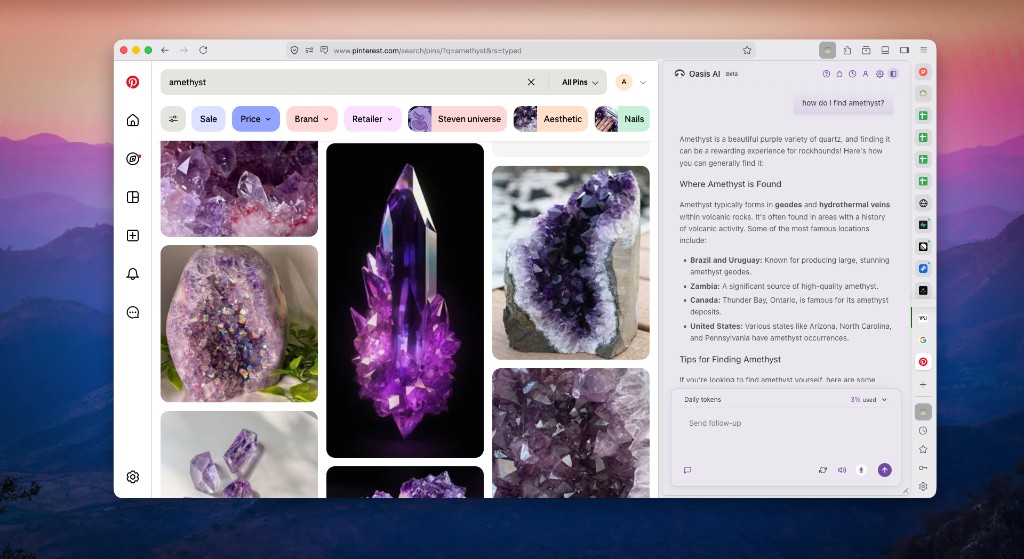
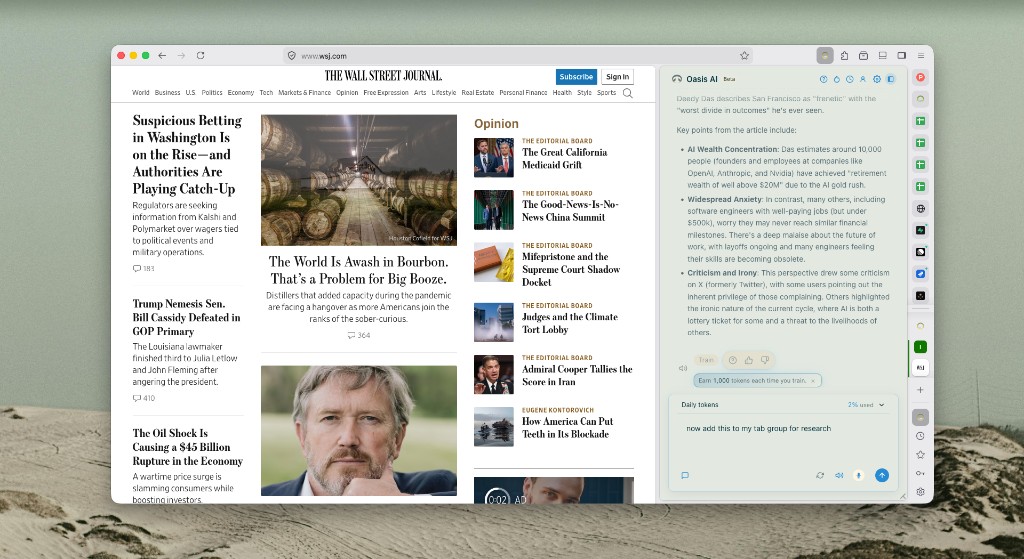
Assistant
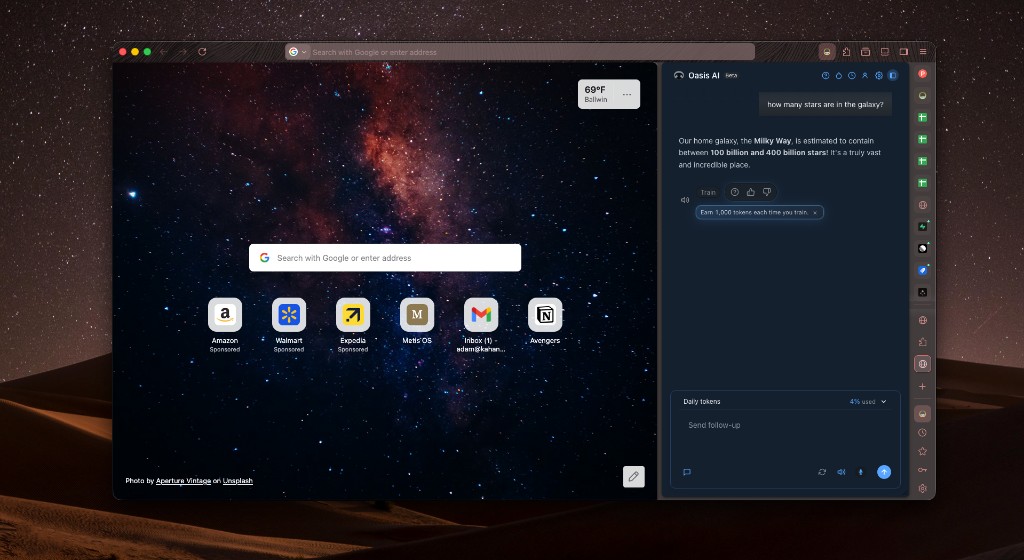
The panel combines a chat timeline, a composer with "Ask Oasis…", read-aloud and feedback on the latest AI message, and readable busy states when a tool is running (for example, summarizing a page). Search and filter below to explore commands and skills: illustrative prompts, not an exhaustive list.
What can Oasis do?
Search in plain language to match ideas like "that article from Tuesday" or "clean up my tabs", then browse example prompts for each area.
Try asking
Filter by category
Tabs and windows
List, open, close, move, and organize tabs and windows without digging through menus.
Example prompts
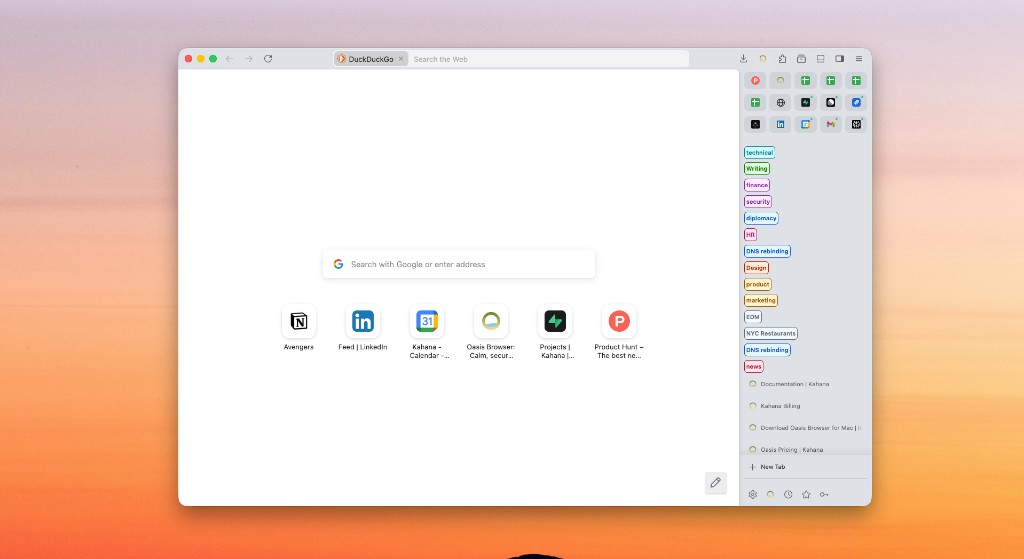
Tab groups
Create, rename, add or remove tabs, and list groups so a messy session stays scannable.
Example prompts
Bookmarks
Treat bookmark folders as first-class: list, create, rename, add tabs, open sets of saved pages.
Example prompts
History
Find pages by meaning—not only exact keywords—when you half-remember a visit.
Example prompts
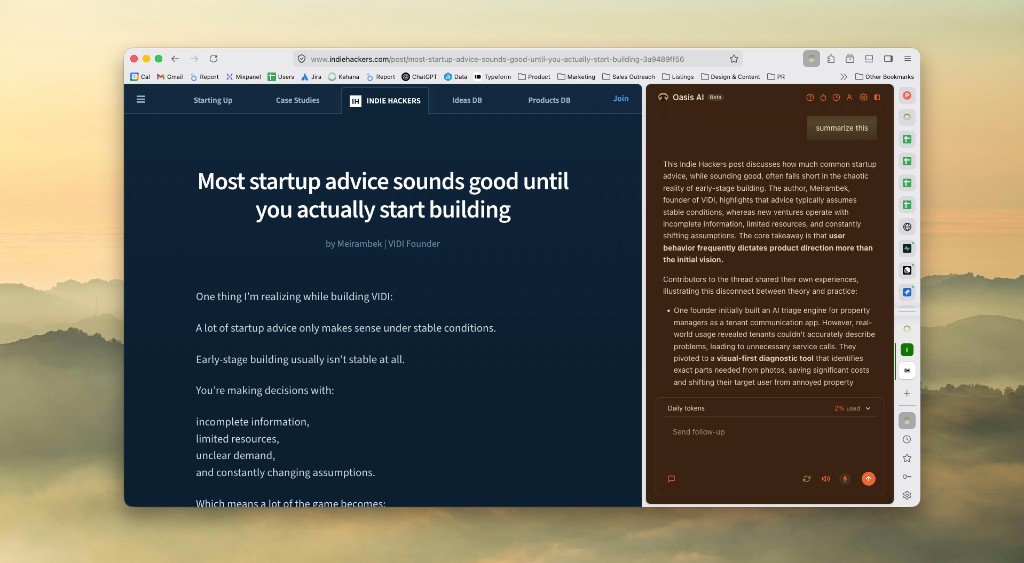
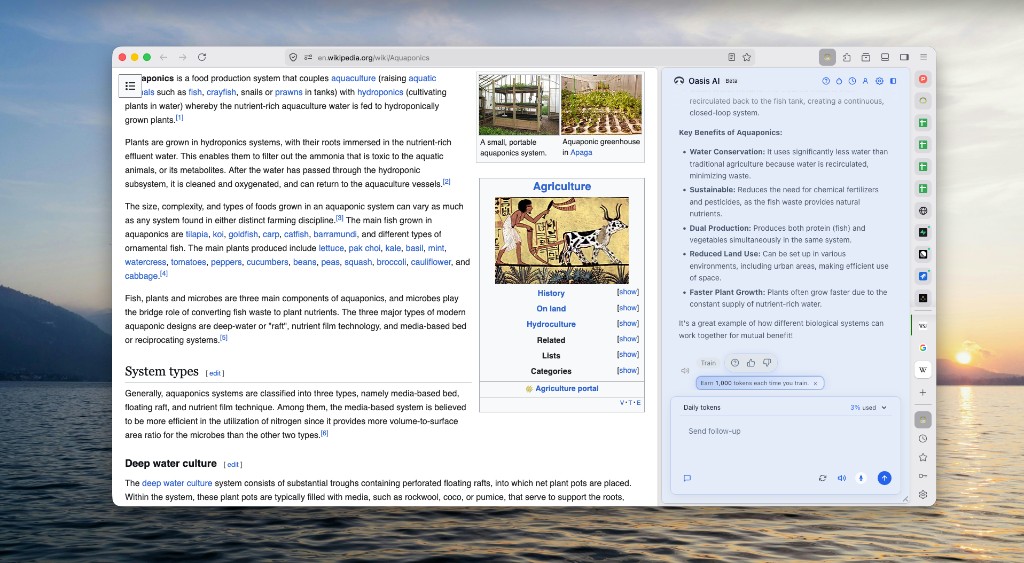
Page understanding
Turn long articles into short answers grounded in what you are viewing.
Example prompts
Saved context
Search across what the assistant can access, including saved and visited context.
Example prompts
Showing 1–6 of 7
Personalization
Pick light or dark schemes for the assistant panel. Themes affect assistant chrome only—not the colors of the web pages you browse.
Control
When a command could change your browsing state in a meaningful way, Oasis can ask you to confirm. You see plain-language copy plus a highlighted command line so you know exactly what will run.
Illustrative modal below. Real copy and icons may vary slightly by version.
This will close a tab and cannot be undone from the assistant. Continue?
Onboarding
A docked checklist tracks basics like signing in, sending a first prompt, and trying voice, so you are not left wondering what to do after install.
Switching
Oasis uses a migration-style wizard so you are not rebuilding your digital life from scratch. One guided flow, clear choices, and OS permission prompts only when needed. Switching often takes seconds, not minutes.
General
Bring your bookmarks, passwords, history, extensions, and autofill data from another browser.
Coming soon
Planned feature: tags, notes, and thumbs become the loop that steadies the assistant over time. Preview below.
Read the full Amplifier guide →
Most assistants miss the mark on real work: too slow, too wrong, or tuned for demos. Training in Oasis is where you react in context—tags, notes, thumbs, and flows like training on a specific reply—so we can steer quality toward smarter, more accurate, and faster answers for you. Qualifying training can also add bonus tokens to your daily balance; caps and rules follow your Oasis plan.
Amplifier is the name we use for that whole feedback loop: signal grounded in real conversations, not vibes. Today that signal is tied to your account and the interaction you rate. Later, we plan explicit anonymous and personalized training modes so you can choose how much identity rides with the payload—roadmap, not a promise of ship dates.
Consistent, specific feedback over 30, 60, and 90 days is the shape of the compounding story below. The chart is illustrative only, not a live dashboard or guarantee for your curves.
Train & react
Simplified mock for layout; see the Amplifier & Training feature page for real in-app captures.
Help us improve Oasis
Did we get it right?
Illustrative trajectory
Concept only: as Training piles up, we expect the assistant to feel sharper, steadier, and quicker on the work you actually do. The three lines are placeholders for speed, accuracy, and overall quality—not a guarantee, live dashboard, or your measured trajectory.
| Day | Speed | Accuracy | Quality |
|---|---|---|---|
| Day 1 | 28 | 22 | 24 |
| Day 30 | 52 | 48 | 50 |
| Day 60 | 74 | 76 | 78 |
| Day 90 | 90 | 92 | 94 |
Comprehensive answers to technical and business questions
Work with multiple applications simultaneously